Organizations deploying iPhones or iPads for frontline staff, shared workstations, retail, logistics, or kiosk scenarios often struggle with the same question:
Should we use Microsoft Shared Device Mode, or Apple Shared iPad for Business?
Both solve “shared use” problems, but they work very differently, especially when combined with Microsoft Intune, Microsoft Entra ID, Conditional Access, and App Protection Policies.
This post breaks it down with a clear, real-world comparison. Recently, I’ve been working with several organizations deploying shared devices, and the same questions keep coming up around user experience, identity behavior, and which shared model is the right fit.
I’ll also be sharing a separate, step-by-step post soon on how to set up the profiles in Intune and what the user experience actually looks like on each device type.

Table of Contents
What is Microsoft Shared Device Mode (SDM) for iOS?
Shared Device Mode is a Microsoft Entra identity feature that turns an Intune-enrolled iOS device into a single-user-at-a-time, multi-shift device. It is specifically designed for frontline workers who “sign in → perform tasks → sign out.”
Key characteristics
- Uses Microsoft Authenticator + Shared Device Mode toggle
- Only one user is signed in at a time
- “Global logout” signs the user out of all participating apps
- Supports Microsoft first-party apps (Teams, Outlook, Edge, PowerApps, Viva, etc.)
- Works with Entra Conditional Access
- No Apple multi-user framework involved
- No local user profiles
Use Cases
- Warehouse or retail devices
- Healthcare shared iPhones
- Hot desk iPads where users authenticate for short sessions
- Devices used only for cloud apps, not personal apps
What is Apple Shared iPad for Business?
Shared iPad for Business is an Apple-native multi-user iPadOS feature, enabled via ADE/DEP. It allows multiple users to have local profiles stored on the device.
Key characteristics
- Multiple user profiles stored locally
- Sign-in uses Managed Apple IDs
- Offline sign-in supported after first login
- Works without Microsoft Authenticator
- Allows persistent user data between sessions
- Full iPadOS multi-user experience
- Apps installed for the device, not per user
Use Cases
- Education
- Training centers
- Multi-user tablets that keep session data
- Environments with low dependency on Microsoft identity
Enrollment and Setup Differences
Shared Device Mode enrollment
- ADE profile using “Shared Device Mode” in Intune
- The device automatically joins Entra as a Shared mode device
- Supported Devices: iPhone, iPod touch, iPad
- Authenticator automatically configures SDM (no manual registration needed)
- No Apple ID required
- Zero local user persistence
Shared iPad enrollment
- ADE profile set as Shared iPad for Business
- Supported Devices: iPad only
- Requires Managed Apple IDs
- Optional temporary session user
- Storage quota per user
- Local profile persistence
- Works even when offline
Feature Comparison: Shared Device Mode vs Shared iPad
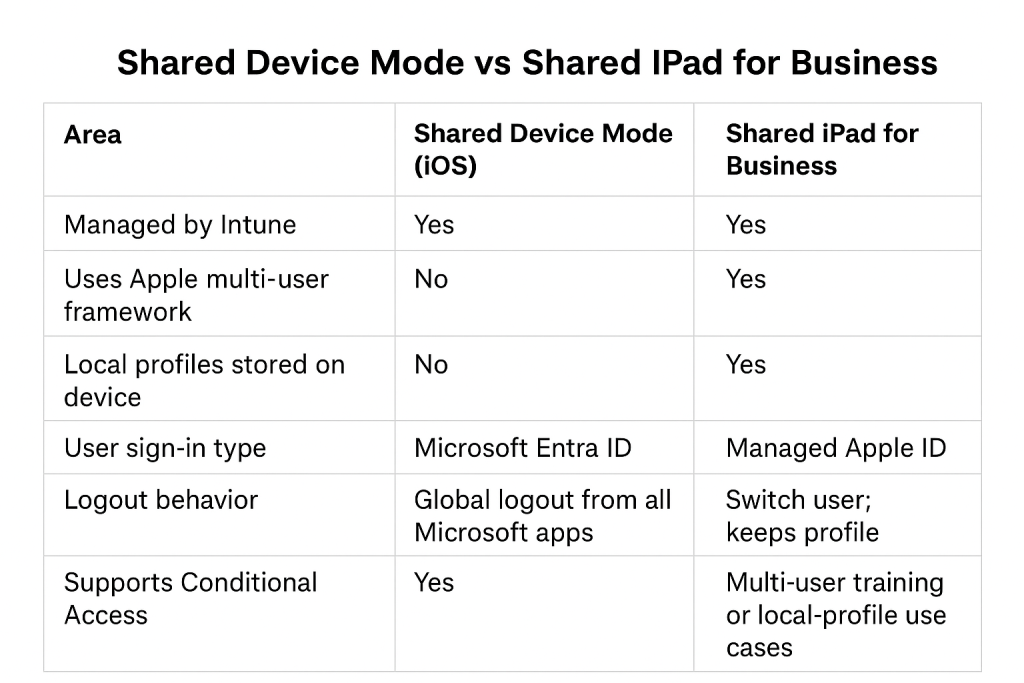
Conditional Access: Major Differences
Shared Device Mode
SDM provides the cleanest Conditional Access integration because:
- Microsoft apps understand the “shared device mode” context
- CA can evaluate Entra ID sign-in + device state
- Device shows as MDM compliant / enrolled
- Filters like device.trustType work as expected
- Cloud apps behave consistently across sign-ins
Shared iPad Conditional Access behavior
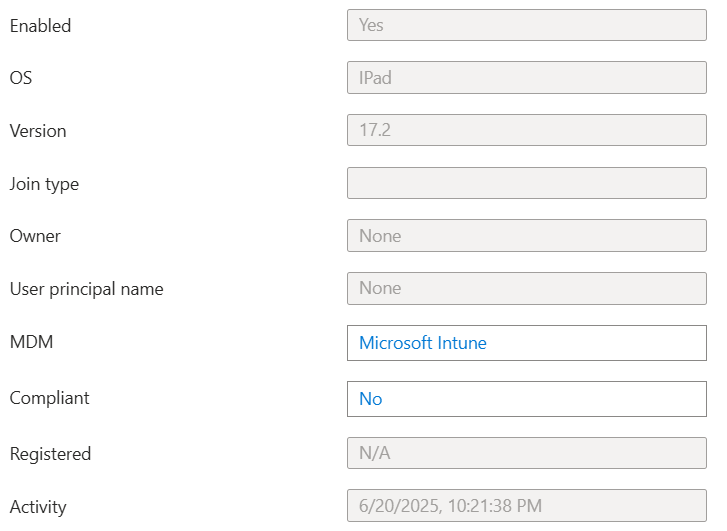
One ongoing frustration is that Conditional Access does not fully support Shared iPads, and this is one of the most common complaints I hear from organizations. Many want to block access from unmanaged devices, but Shared iPads are often categorized as unmanaged and end up being blocked unintentionally.
Problem:
Shared iPads authenticate into Entra using browser SSO or app tokens, but these are tied to the Shared iPad session, not a device-bound identity. Therefore Conditional Access often sees these as “unmanaged devices”, especially when apps use web auth (MSAL + broker behavior differs).
This explains errors like:
- “Your device is not compliant”
- “Unmanaged device blocked”
- Or device.trustType = None
Below is an example screenshot of the object in Entra, showing its properties. Take note of the following device filters, which cannot be used in Conditional Access.
- Join type: blank
- Complaint: NO
- Registered: N/A
Management Experience in Intune
Shared Device Mode
You manage SDM iPhones/iPads like any supervised company-owned device:
- Device restrictions
- App deployments
- Compliance policies
- SSO plug-in
- Managed app configs
- Remote actions (wipe, restart, rename, etc.)
Great for environments where:
- Everything runs through Microsoft login
- Tight CA is required
- Zero user persistence is desirable
Shared iPad
Intune manages Shared iPads as a single MDM-enrolled device, not per user.
That means:
- Profiles apply to the whole device
- App installs go to the device, not per user
- CA treats authentications as user-only, device unknown
Which Should You Choose?
I can highlight some key points below, but ultimately it depends on your organization’s requirements. Specifically for Shared iPads, I’ve seen organizations that want the login/logout feature while also enforcing strict Conditional Access policies. Unfortunately, Shared iPads are categorized as unmanaged devices, which makes them difficult to work with in environments that have extensive restrictions. I will follow up with posts that provide more details on Shared Device Mode, Shared iPad setup, and the overall user experience.
Choose Shared Device Mode if…
- You rely heavily on Microsoft apps (Teams, Outlook, PowerApps)
- Conditional Access must enforce compliance
- You want easy login/logout
- No user data persistence is required
- You want cleaner Entra + Intune integration
Choose Shared iPad if…
- Great for education, kiosks or training facilities.
- You need Apple’s multi-user experience
- Profiles need to persist across logins
- Managed Apple IDs are already deployed
- Offline usage is required
- Microsoft apps are not the primary apps
References
Shared Device Mode – https://learn.microsoft.com/en-us/entra/identity-platform/msal-shared-devices
Shared iPad – https://learn.microsoft.com/en-us/intune/intune-service/enrollment/device-enrollment-shared-ipad
Overview of shared device solutions for iOS/iPadOS – https://learn.microsoft.com/en-us/intune/intune-service/enrollment/device-enrollment-shared-ios